Compliance risk assessments help organizations identify and manage risks tied to legal and regulatory requirements. Unlike security assessments, these focus on avoiding penalties, contract breaches, and enforcement actions. With stricter rules like the SEC's 4-day incident reporting and the FTC's expanded Safeguards Rule, businesses need a clear, structured process to stay compliant.
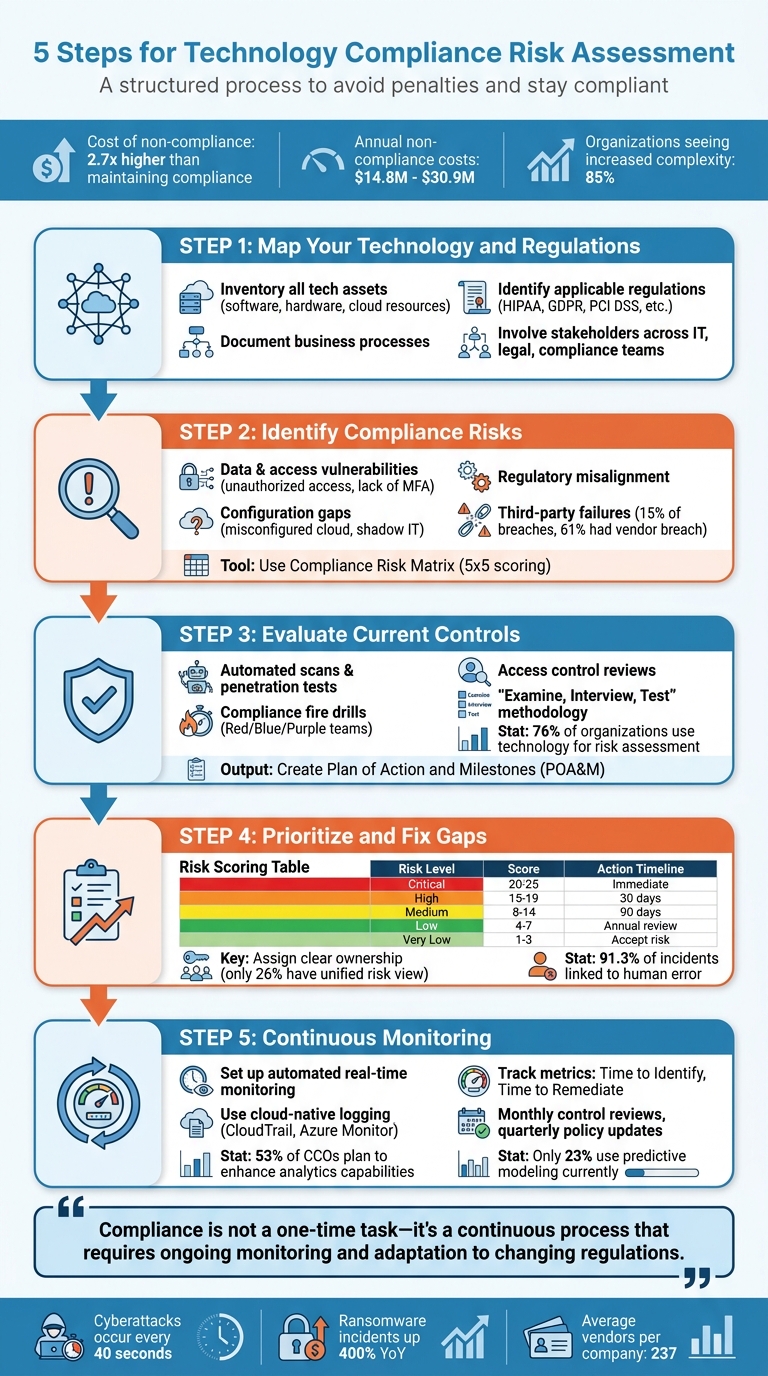
Here’s a quick breakdown of the 5 steps:
- Map Your Technology and Regulations: Inventory all tech assets, processes, and their regulatory requirements (e.g., HIPAA, GDPR, PCI DSS).
- Identify Compliance Risks: Pinpoint vulnerabilities like misconfigurations, access issues, or third-party failures.
- Evaluate Current Controls: Test your controls with audits, scans, and simulations to find gaps.
- Prioritize and Fix Gaps: Rank risks by impact and urgency, then create action plans to address them.
- Continuous Monitoring: Use tools for real-time tracking and adapt to changing regulations.
This process ensures compliance becomes a continuous effort, reducing risks and aligning with business goals.
5 Steps for Technology Compliance Risk Assessment Process
Compliance Risk Assessments
sbb-itb-97f6a47
Step 1: Map Your Technology Environment and Regulatory Requirements
To build a solid compliance risk assessment, the first step is understanding what you're protecting and the rules you need to follow. Rajesh Nair, Managing Director at TechCloudPro, sums it up well:
Risk cannot be assessed without knowing what you are protecting.
This foundational mapping is key to identifying compliance risks in the steps that follow.
Document Your Technology Assets and Processes
Start by creating a detailed inventory of your technology environment. This means listing all your software, hardware, components, and data storage systems - whether they're on-premises servers or cloud-based resources like databases, storage buckets, compute instances, and API endpoints. Don’t stop there; include the business processes tied to these systems, such as payroll, customer service, order management, and research workflows.
For each asset, gather critical details like ownership, classification level (e.g., public, internal, confidential, or restricted), system dependencies, and business importance. Understanding system dependencies is crucial for evaluating cascading risks. Don’t overlook third-party assets like vendors, managed service providers, or sub-processors, as their vulnerabilities can directly affect your compliance.
Focus on systems that are critical to your operations. To keep everything up-to-date, consider integrating your IT infrastructure with a Configuration Management Database (CMDB) for real-time tracking. Collaborate with teams across your organization - IT, HR, Legal, Sales - to ensure you capture how data flows throughout your business. NIST SP 800-53 Rev 5 control CM-8 emphasizes the importance of maintaining an accurate inventory to reliably assign controls.
With this comprehensive map of your technology assets, you can begin aligning them with the relevant regulations.
Determine Which Regulations Apply
Next, figure out which regulations apply to your specific assets. This depends on the type of data you handle, your industry, and where your customers or data subjects are located. For example:
- If you process Protected Health Information (PHI), you'll need to comply with HIPAA.
- Handling payment card data? That means PCI DSS applies.
- Serving European customers? You’ll need to meet GDPR requirements.
Additionally, frameworks like NIST CSF, CIS Controls, ISO/IEC 27001:2022, SOC 2, and FedRAMP may apply based on your industry and data types. Keep an eye on regulatory updates, such as the FTC Safeguards Rule (effective June 9, 2023) or the SEC’s new cybersecurity disclosure rules, which require incident reporting within four business days.
It’s important to remember that even if your cloud provider complies with certain regulations, the responsibility for data classification, access controls, and application configurations still falls on you.
Once you’ve identified the relevant regulations, bring in the right people to help you align your compliance strategy.
Involve the Right Stakeholders
Mapping your technology environment isn’t something IT can handle alone - it requires input from multiple teams. Bring together IT, security, compliance, legal, business leaders, and, when needed, external experts to ensure both technical and regulatory perspectives are covered.
As Hyperproof explains:
Information security should ideally involve two groups: senior management and IT staff. Senior management should dictate the appropriate level of security, while IT should implement the plan to help achieve that level of security.
Assign ownership for every asset or risk you identify, ensuring there’s someone responsible for its management and remediation. Use frameworks like NIST or ISO to create a shared language that makes technical findings understandable and actionable for leadership. For smaller organizations, hiring external specialists like a Virtual CISO (vCISO) can provide expert guidance and bring consistency to your risk assessments.
Step 2: Identify Technology Compliance Risk Points
Once you've mapped out your systems, the next step is to zero in on specific compliance risk points - both within your own operations and across third-party relationships. This targeted approach helps you address vulnerabilities more precisely.
What Counts as Compliance Risk in Technology
Compliance risks in technology can be grouped into several areas:
- Data and access vulnerabilities: These include unauthorized access to sensitive systems, lack of Multi-Factor Authentication (MFA) on critical entry points like VPNs, and inadequate encryption for data at rest or in transit.
- Configuration and asset gaps: Misconfigured cloud resources are a major issue - often the most exploited enterprise vulnerability. "Shadow IT" also poses risks, as employees may use unauthorized cloud services without IT's approval. Unpatched software and systems further widen the risk landscape.
- Regulatory and policy misalignment: This happens when your operations don't meet the requirements of regulations like GDPR, HIPAA, or PCI DSS. Misunderstanding shared cloud responsibilities is a common pitfall here.
- Third-party failures: These occur when vendors or sub-processors handling your regulated data experience compliance breaches.
The numbers paint a concerning picture. The 2023 Verizon Data Breach Investigations Report found that 15% of all data breaches involved a third party. Even more troubling, 61% of companies reported a third-party-related security breach between 2023 and 2024, marking a 49% increase from the previous year.
Use a Compliance Risk Matrix
A compliance risk matrix is a practical tool that helps you prioritize risks by evaluating their likelihood and potential impact. This visual framework clarifies which vulnerabilities need urgent attention and which can be addressed later. As DataGuard puts it:
A compliance risk assessment matrix is a practical, hands-on tool that helps organisations pinpoint, assess, and manage their risks effectively.
A typical 5x5 matrix scores risks from 1 to 25. Risks scoring between 20 and 25 are categorized as "Critical." These usually require a treatment plan within 48 hours and remediation within 30 days. For example, if your production database containing Protected Health Information (PHI) lacks encryption at rest, you'd assess the likelihood of exploitation as "Likely" (4) and the impact as "Critical" (5), resulting in a total risk score of 20. This score signals an immediate need for action.
The matrix connects technical vulnerabilities to business outcomes. For instance, if your VPN lacks MFA, the matrix helps articulate the risk in business terms: what's the probability of unauthorized access, and what would be the financial or regulatory fallout if it occurred?
Evaluate Vendor and Third-Party Risks
Your internal systems aren't the only concern - third-party vendors can also pose major compliance risks. Start by cataloging all vendors and classifying them into risk tiers. Consider factors like the sensitivity of the data they handle, their access level, and their importance to your operations.
- Tier 1 vendors: These are the most critical, handling sensitive data such as PHI, PII, or payment card information. For these vendors, you'll need thorough security questionnaires, SOC 2 Type II reports, and legal agreements like Data Processing Agreements (DPA) under GDPR or Business Associate Agreements (BAA) under HIPAA.
Before signing any contracts, demand documented proof of vendor compliance. Use standardized tools like the SIG (Standardized Information Gathering) or CAIQ (Consensus Assessments Initiative Questionnaire) to evaluate their security posture. Also, ensure their SOC reports are current - a SOC report ending June 30 may not suffice for a December 31 fiscal year-end audit without a bridge letter.
Skipping vendor due diligence can have costly consequences. Advocate Health Care learned this the hard way, settling with the Office for Civil Rights for $5.55 million after failing to secure BAAs from vendors who later experienced breaches. Additionally, not having a HIPAA-compliant BAA can result in fines of up to $71,162 per violation per year. With companies working with an average of 237 vendors, and with vendor risk assessments quickly becoming outdated - 67% of sub-processor pages and 41% of privacy policies changed within 90 days - continuous monitoring is essential.
Step 3: Assess and Evaluate Existing Controls
Once you've pinpointed compliance risk areas, the next logical step is to evaluate how well your existing controls are performing. As Centric Consulting cautions:
Merely checking the boxes gives you the illusion of covering all of your bases, but in many cases, it's merely the beginning.
Test How Well Your Controls Work
Start by putting your defenses to the test. This includes technical evaluations like automated scans, penetration tests, and simulated phishing campaigns to gauge how effectively your systems hold up under real-world conditions. You can also run compliance fire drills, using Red, Blue, and Purple team exercises, to see how well your teams detect, respond to, and contain incidents. Don’t overlook access controls - review active accounts to spot orphaned accounts left behind by former employees or vendors. Benchmark your performance against industry standards to identify any weak spots.
The trend toward continuous monitoring is gaining momentum. Currently, 76% of organizations use technology specifically for risk assessment. Tools like Security Information and Event Management (SIEM) and Cloud Security Posture Management (CSPM) allow for real-time compliance tracking, moving away from outdated, periodic audits. However, only 23% of Chief Compliance Officers are using advanced tools like data analytics and predictive modeling for ongoing compliance monitoring.
Once you've completed technical testing, shift gears to identify and document any gaps in your compliance program.
Find Gaps in Your Compliance Program
A structured approach like the "Examine, Interview, Test" methodology can help uncover gaps in your compliance program. Start by examining key documentation, including policies and system logs. Follow this with interviews to confirm that processes are being followed as intended. Finally, test controls to ensure they are functioning correctly.
Once you've identified operational gaps, organize your findings by linking them to specific regulatory requirements. A control mapping matrix can help here - this tool matches regulatory clauses to your internal controls, highlighting which requirements are fully addressed, partially covered, or completely missing. Use a maturity scale - "Fully Implemented", "Partially Implemented", or "Not Implemented" - to rate each control and assess the severity of any gaps.
Be mindful of configuration drift, where technical controls evolve over time and stray from your original compliance baseline. For example, in cloud environments, your provider’s compliance certifications don’t automatically cover your responsibilities, such as managing encryption keys or classifying data properly.
Document all findings in a Plan of Action and Milestones (POA&M). This document should track unresolved gaps, assign owners, and set clear remediation deadlines. It’s also important to define what qualifies as a "material" gap based on your industry and organizational size, so you don’t waste resources on minor issues.
Link Controls to Specific Risks
Tie your control evaluations back to your earlier risk mapping to maintain a full compliance picture. Linking controls to specific risks helps translate technical findings into business terms that leadership can easily understand. This approach quantifies how effective your controls are and highlights any residual risk. It also ensures that your security investments address real threats instead of just checking procedural boxes.
Maintain a detailed risk register that connects every control gap to its related regulation, risk score, and assigned owner. You can classify controls into these types:
| Control Type | Function | Examples |
|---|---|---|
| Preventive | Prevents violations before they occur | MFA, encryption, firewalls, access controls |
| Detective | Identifies violations when they happen | Audit logs, vulnerability scans, IDS |
| Administrative | Guides human behavior | Security policies, employee training, incident response plans |
To prioritize remediation efforts, use a qualitative scoring matrix (e.g., 3x3 or 5x5) that considers both likelihood and impact. Also, map dependencies between IT assets to understand how a single control failure could trigger cascading effects. Governance, Risk, and Compliance (GRC) platforms can centralize this mapping and provide real-time visibility, a feature already used by 49% of organizations for 11 or more compliance activities.
The benefits of this approach are clear: only 26% of organizations currently have a unified view of risk across the business. By linking controls to risks, you create an audit trail and help leadership see the value of focused security investments.
Step 4: Prioritize and Address Compliance Gaps
After identifying control gaps in Step 3, the next step is to prioritize and address them. Not all compliance risks demand the same level of attention, and spreading resources too thin can leave critical vulnerabilities exposed. Here's a staggering fact: the cost of non-compliance is 2.7 times higher than maintaining a proper compliance program, with annual costs ranging from $14.8 million to $30.9 million. Prioritizing risks ensures you focus on what matters most.
How to Prioritize Compliance Risks
Start by revisiting your risk assessments and applying a standardized 1-5 scoring scale for both likelihood and impact. This consistent approach helps align evaluations across departments. Here’s how it works:
- Likelihood scores: Ranges from 1 (Very Low: <5%) to 5 (Very High: >65%)
- Impact scores: Uses financial thresholds, such as 1 (Very Low: <$50,000), 3 (Medium: $500,000–$5 million), and 5 (Very High: >$50 million).
To calculate a composite risk score, multiply the likelihood score by the impact score. For instance, a risk with a likelihood of 4 and an impact of 5 would score 20 on a 25-point scale. Use this score to prioritize risks and map them visually on a color-coded risk heatmap (green, yellow, red) for executive review. Here's a quick breakdown:
| Risk Level | Composite Score | Action Required |
|---|---|---|
| Critical Risk | 20 – 25 | Immediate action required |
| High Risk | 15 – 19 | Action required within 30 days |
| Medium Risk | 8 – 14 | Action required within 90 days |
| Low Risk | 4 – 7 | Monitor and review annually |
| Very Low Risk | 1 – 3 | Accept risk level |
To refine scores further, consider risk velocity (how quickly a risk can escalate) and regulatory attention multipliers for risks under heightened scrutiny. For example, in May 2023, Meta faced a record-breaking €1.2 billion GDPR fine for improper data transfers from the EU to the US. This demonstrates how regulatory focus can amplify the consequences of compliance gaps.
Given that 85% of organizations report increasing complexity in compliance requirements over the last three years, clear visualization tools like heatmaps are essential for decision-making. Adjust scores based on control maturity - a high-risk item with strong, automated controls may rank lower. In cloud settings, remember the Shared Responsibility Model, where providers handle infrastructure security, but you’re still accountable for data classification and access controls.
Create Action Plans to Fix Gaps
Once risks are ranked, decide on the appropriate response: remediate (fix the issue), mitigate (reduce the risk), transfer (via insurance or third-party contracts), or accept (formally acknowledge residual risk). Start with the highest-ranked risks and work down.
Document all actions in your POA&M (Plan of Action and Milestones), tracking unresolved gaps with realistic timelines that balance urgency with business needs. Chief Ethics and Compliance Officers often allocate their budgets to cybersecurity and data privacy (59%), advanced data analytics (50%), and process automation (48%).
Use quantitative data to showcase ROI to leadership, emphasizing how compliance investments reduce potential fines and improve operations. Identify areas needing upskilling or new tools to address technical gaps. If remediation delays business operations, ensure residual risks are formally accepted, quantified, and documented per company policy.
Finally, consolidate all findings in a centralized risk register. This should include details like the control gap, relevant regulation, risk score, and assigned owner. This register becomes the go-to resource for auditors and leadership.
Assign Clear Responsibilities
Compliance failures often stem from unclear accountability. Jill Henriques, GRC Subject Matter Expert at Vanta, emphasizes:
Compliance failures are often rooted in people risks, especially unclear accountability. Without defined roles and ownership for prioritizing compliance-related tasks, organizations will struggle to meet requirements consistently.
Assign a specific owner and timeline to every action item in your remediation plan. Responsibilities should be distributed among senior leadership (CIO, CTO, CISO), compliance leaders, and operational managers who understand the potential impact of system disruptions. Asset and control owners handle the technical and administrative aspects of compliance.
Engage cross-functional teams from operations, finance, and legal, and use automated tools to ensure recurring reviews happen on schedule. Alarmingly, only 26% of organizations have a shared view of risk across their business, creating blind spots.
Prepare formal reports for senior management, highlighting high-priority risks and recommended timelines for action. Each risk should have a documented decision - whether mitigated, accepted, transferred, or avoided. Leaving a risk undecided undermines the entire process. Organizations with limited internal resources can benefit from hiring a virtual CISO (vCISO) to oversee planning and maintain consistency across compliance cycles.
With 91.3% of compliance-related incidents linked to human error, clear ownership and accountability are non-negotiable. Properly assigning roles now sets the stage for effective ongoing monitoring in the next step.
Step 5: Implement Monitoring and Continuous Assessment
Compliance isn’t a one-and-done task - it’s an ongoing process. Once your risk framework and controls are in place, continuous monitoring ensures that your compliance efforts stay effective even as your environment evolves. Instead of relying on outdated, periodic audits, continuous compliance monitoring uses automated, real-time assessments to evaluate control states against regulatory frameworks. This is especially important in cloud environments, where rapid changes like auto-scaling or infrastructure-as-code deployments can render manual checks outdated in mere hours.
Set Up Regular Monitoring Procedures
To keep compliance on track, set up a monitoring system that collects essential data (like telemetry or API polling), evaluates policies using machine-readable rules, and scores findings by severity. This system should also integrate reporting with remediation efforts. Use cloud-native logging tools, such as AWS CloudTrail, Azure Monitor, or GCP Cloud Audit Logs, to keep an eye on configuration, identity, and data compliance. Tools like Open Policy Agent (OPA) or AWS Config Rules can help translate complex legal requirements into executable logic. These tools enable automated fixes for smaller issues - like overly open storage buckets - reducing the need for manual intervention and lightening the compliance workload.
Key metrics to track include "Time to Identify" and "Time to Remediate", and it’s important to conduct reviews whenever significant changes occur. As Michael Condon, Manager of Compliance Solutions at Optro, puts it:
Compliance is not stagnant; new risks are always coming into scope and the regulatory landscape is fluid.
| Metric Category | Metrics |
|---|---|
| Issue Metrics | Time to identify, time to remediate, total open issues, critical impact issues |
| Risk Metrics | Time to mitigation plan, risk treatment type (accepted, mitigated, transferred) |
| Assessment Metrics | Assessment coverage (controls/risks reviewed), time to complete an assessment |
| Overall Compliance | Compliance status by framework, percentage compliant with new frameworks |
With these systems in place, you’ll be ready to adapt to changes in compliance requirements as they arise.
Adjust to Changing Compliance Requirements
Regulatory landscapes are constantly shifting, and your compliance strategy needs to keep up. A recent report found that 85% of organizations have seen compliance requirements grow more complex over the past three years. Unsurprisingly, 77% of those organizations say this complexity has hurt their growth. To stay ahead, schedule monthly control reviews and quarterly policy updates to catch “compliance drift” - when your policies stop aligning with current regulations. Use living documents with triggers tied to regulatory updates or operational changes to stay proactive. Automated tracking systems can further help by flagging controls affected by new mandates.
Technology plays a critical role here. Over half (53%) of Chief Compliance Officers plan to enhance their technology and data analytics capabilities, and 63% expect budget increases for automation and AI. Collaborate with IT to ensure your data infrastructure is solid and supports strong data governance. Accurate, accessible data is critical for effective compliance monitoring, yet only 23% of organizations currently use data analytics or predictive modeling for this purpose.
Once your metrics are reviewed and your compliance strategy is adjusted, it’s time to document and report your findings.
Document and Report Your Findings
Proper documentation creates a clear audit trail for both regulators and stakeholders. Use a standardized risk taxonomy or the Common Vulnerability Scoring System (CVSS) to classify findings and prioritize remediation. Link each finding to a specific control identifier, such as NIST SP 800-53 or ISO 27001, to provide clear context for audits. Centralizing compliance data with a GRC platform can give you enterprise-wide visibility into risks. These platforms can also align monitoring outputs with the evidence needed for audits like SOC 2 or FedRAMP.
Set a regular reporting cadence: for example, monthly vulnerability scan results for technical teams and quarterly summaries for executives. Maintain a Plan of Action and Milestones (POA&M) to track remediation progress. When presenting to leadership, include measurable outcomes, such as fines avoided or sales enabled, to justify compliance investments. Lastly, clearly differentiate which controls are managed by your cloud provider versus those handled internally to avoid reporting gaps.
Continuous monitoring doesn’t just keep you prepared for audits - it builds trust with regulators. As NIST SP 800-137 explains:
maintaining ongoing awareness of information security, vulnerabilities, and threats to support organizational risk management decisions.
Tools and Resources for Technology Compliance Risk Assessment
After identifying and prioritizing compliance risks, the next step is choosing the right tools and expert support to ensure your assessment process stays effective. Modern tools not only streamline compliance efforts but also centralize data and integrate multiple frameworks. For instance, GRC (Governance, Risk, and Compliance) platforms are designed to automate compliance tasks and consolidate evidence collection. Tools like OneTrust Tech Risk & Compliance come equipped with over 55 frameworks and 500+ pre-built connectors, giving you a single view of systems, data, and risks with dynamic scoring. Similarly, Mitratech Vendor Risk Assessment offers a library of 800+ templates for standards like SIG, GDPR, and ISO 27001, using AI to extract data from SOC 2 reports automatically.
In addition to GRC platforms, vulnerability scanners such as Nessus, Qualys, or Rapid7 help pinpoint technical weaknesses in your infrastructure. Tools like LeanIX, an enterprise architecture (EA) platform, provide a comprehensive view of your IT environment and its interdependencies. These solutions integrate smoothly into your risk assessment framework, boosting both accuracy and efficiency.
Software Tools for Compliance Assessment
When evaluating compliance tools, prioritize platforms with features like automated evidence collection, multi-framework mapping, and real-time monitoring. With nearly half of organizations (49%) using technology for 11 or more compliance activities, integration becomes a key consideration. A robust toolset should include:
- Vulnerability scanners to address technical gaps
- GRC platforms for centralizing documentation and mapping controls
- Cloud Security Posture Management (CSPM) tools for ongoing cloud compliance monitoring
Many platforms now support quantitative risk models, allowing risks to be expressed in financial terms. This can be particularly useful when justifying compliance investments to leadership.
Frameworks like NIST RMF rely on qualitative risk ratings, making them suitable for federal contractors. On the other hand, ISO 27005 offers both qualitative and quantitative methods, ideal for organizations aiming for ISO 27001 certification. For financial risk translation, FAIR v3.0 helps quantify risks in dollar values, making it easier to communicate with executives. The right tool for your organization will depend on your regulatory requirements, technical setup, and risk management strategy.
Work with Consulting Experts
While automated tools are essential, consulting experts add significant value by turning technical findings into actionable plans. Professional consultants can guide your compliance strategy, especially during critical transitions like mergers, acquisitions, or cloud migrations.
As Maggie Paulk Welch from Hyperproof points out:
If your firm does not have security and compliance subject matter experts on staff... it is crucial to seek out assistance from professional services firms that have deep expertise in addressing IT security issues.
Engaging a Virtual Chief Information Security Officer (vCISO) team is another option. This approach provides ongoing support without overburdening internal teams. Joshua Kuntz, a vCISO at Vistrada, explains:
vCISO engagements can provide this repeatability and continuity without overloading the organization's internal capacity.
Consultants are particularly helpful in crafting remediation roadmaps, assigning responsibilities, and setting achievable timelines. The Top Consulting Firms Directory (https://allconsultingfirms.com) is a resource for finding firms specializing in IT, cybersecurity, risk management, and digital transformation.
Given that only 26% of organizations report having a unified view of risk, external experts play a critical role in bridging the gap between senior management and IT teams. They help justify resource allocation and align compliance efforts with business goals. Whether it's implementing technical controls like encryption or developing policies and physical security measures, consulting firms bring the expertise needed to establish a strong compliance foundation.
Conclusion
Main Points to Remember
Technology compliance risk assessment is a structured approach to shielding your organization from fines and security threats. The process follows a five-step framework:
- Mapping your technology landscape and understanding regulatory requirements
- Identifying areas of compliance risk
- Evaluating the effectiveness of current controls
- Addressing any gaps by prioritizing them
- Establishing continuous monitoring practices
What ties it all together is aligning technical findings with business priorities. As Joshua Kuntz, vCISO at Vistrada, puts it:
The answer [to why one IT risk should be fixed before another] should not come from the latest scan result or the most recent audit request. It should come from a defined, ongoing process that weighs likelihood against business impact.
This underscores the importance of focusing on risks with the greatest potential impact on your business. With only 26% of organizations reporting a unified view of risk across departments, creating clear accountability and involving multiple teams can elevate compliance efforts into a strategic advantage. This perspective reinforces the idea that compliance isn't a one-time task - it’s an ongoing responsibility.
Compliance is a Continuous Process
Turning compliance monitoring into a continuous effort ensures your organization stays both nimble and secure. The ever-evolving regulatory landscape, shaped by updates like the SEC’s cybersecurity disclosure rules and the revised FTC Safeguards Rule, demands constant vigilance. Couple that with the fact that cyberattacks occur every 40 seconds and ransomware incidents have skyrocketed by 400% year over year, and it’s clear that one-off assessments won’t cut it. This is especially true in dynamic cloud environments where configurations change daily.
Continuous monitoring isn’t optional - it’s essential. While formal evaluations should happen at least once a year, major events like mergers, new vendor access, infrastructure updates, or security breaches demand immediate reassessments. Utilizing automated tools such as GRC platforms and Cloud Security Posture Management (CSPM) solutions, as highlighted in Step 5, helps keep compliance efforts up to date without overburdening your team. As MetricStream aptly states:
Compliance isn't static - regulations change, and so does your business. To stay ahead of the curve, it's essential to continuously monitor your compliance landscape.
FAQs
How do I know which regulations apply to my tech project?
To begin, identify the specific regulations tied to your industry, location, and the type of data you handle. A structured risk assessment is key here - it helps you match applicable regulations, like industry standards or regional requirements, with your existing controls.
Frameworks such as NIST can provide additional guidance, making it easier to clarify your obligations. By following this method, you ensure that relevant regulations are addressed and compliance is managed efficiently.
What’s the fastest way to score and prioritize compliance risks?
The fastest way to evaluate and prioritize compliance risks is to use a structured risk assessment framework. This approach considers two key factors: likelihood and business impact.
Here’s how it works:
- Score risks: Assess each risk by its likelihood of occurring and the potential impact it could have on your business. This helps pinpoint the most pressing issues.
- Visualize rankings: Use tools like heatmaps or matrices to organize and rank risks clearly. These visuals make it easier to understand priorities at a glance.
- Tackle high-priority risks first: Focus on the risks with the highest scores. This ensures your remediation efforts are efficient and decision-making is more straightforward.
By following these steps, you can create a clear action plan to address compliance risks effectively.
What should I continuously monitor to stay compliant in the cloud?
To maintain compliance in the cloud, it's crucial to regularly assess your cloud environment's control states against relevant regulatory and framework requirements. Key areas to prioritize include configuration states, identity entitlements, data classification, network segmentation, cryptographic posture, and log integrity. Leveraging automated tools can help ensure compliance is monitored in real-time or as close to real-time as possible, keeping your environment secure and aligned with standards.


