When sharing data with third parties, compliance isn't optional - it's a necessity. Regulations like GDPR, CCPA, and the newer DORA and NIS 2 frameworks hold you accountable for how vendors handle your data. Non-compliance can lead to fines up to 4% of global annual revenue. For example, Sephora and Disney faced multimillion-dollar penalties for failing to meet privacy standards.
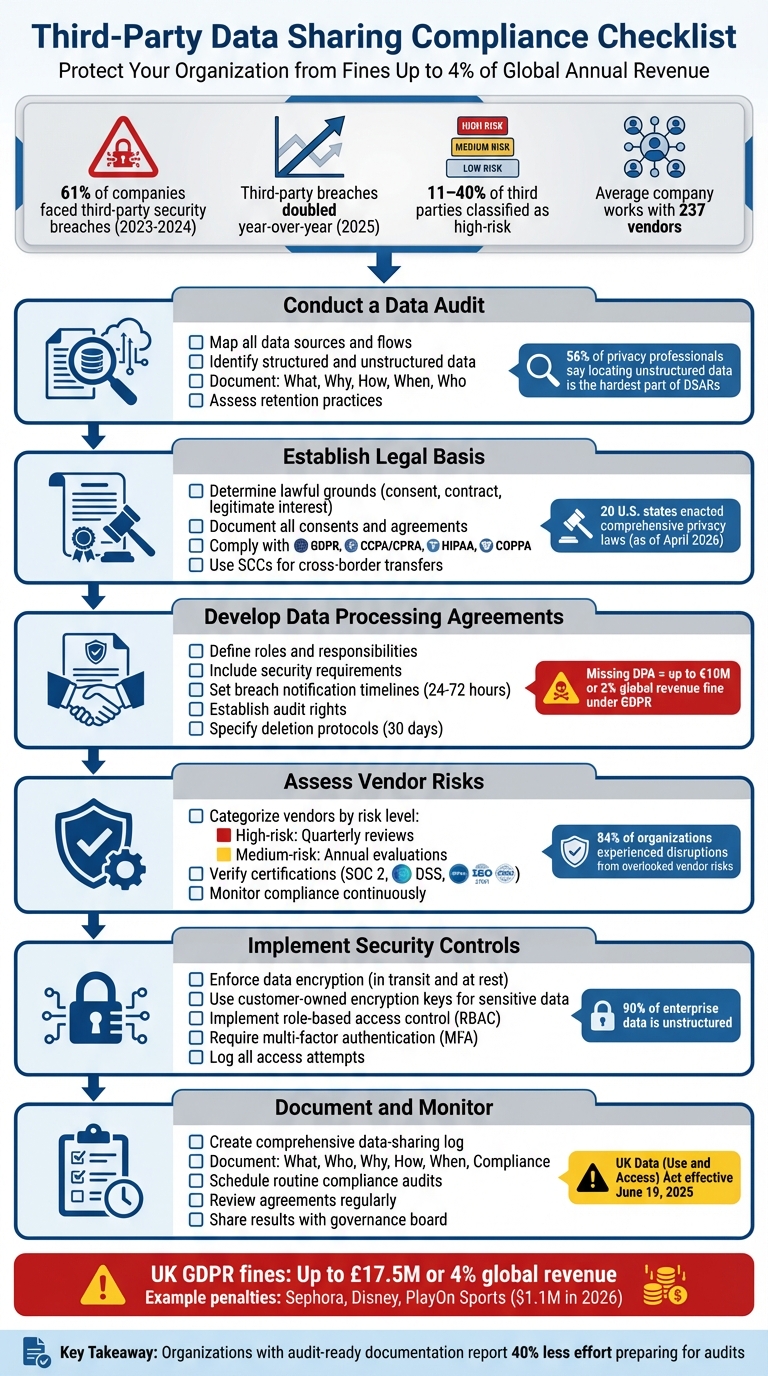
Key Steps for Compliance:
- Audit Your Data: Map all data sources, flows, and retention practices. Identify what data is shared, why, and with whom.
- Establish Legal Basis: Document lawful grounds for sharing, such as consent, contracts, or legitimate interests.
- Draft Data Processing Agreements (DPAs): Clearly define roles, responsibilities, and safeguards with vendors.
- Assess Vendor Risks: Regularly evaluate third-party security measures and certifications like SOC 2 or PCI DSS.
- Implement Security Controls: Use encryption and access management to protect data.
- Monitor and Document Practices: Maintain detailed logs of data-sharing activities and conduct routine audits.
This structured approach helps mitigate risks, align with evolving laws, and maintain trust with customers. Start with a thorough audit and ensure your legal and technical safeguards are airtight.
6-Step Checklist for Third-Party Data Sharing Compliance
Vendor Risk Management - How to Evaluate Third-Party Security Before You Buy
sbb-itb-97f6a47
Step 1: Conduct a Data Audit
A thorough data audit is the cornerstone of ensuring compliance in every subsequent step. Start by identifying and mapping all shared data - this includes everything from customer details in your CRM to employee records stored in your HRIS. Be sure to track both structured data (like databases) and unstructured data (such as email attachments or shared files). Here's why this matters: between 11% and 40% of third parties are classified as high-risk across organizations. And breaches involving third parties have doubled year-over-year, according to the 2025 Data Breach Investigations Report. Clearly, a comprehensive audit is not optional - it’s essential.
Identify Data Sources and Flows
Begin by mapping out all systems that process personal data. For structured data, look at tools like CRM platforms, data warehouses, HRIS systems (e.g., Personio), and payment processors. Unstructured data, on the other hand, flows through less formal channels like email attachments, file-sharing tools, Managed File Transfer (MFT) workflows, shared drives, and communication apps such as Zoom or Intercom.
Interestingly, 56% of privacy professionals say that "locating unstructured personal data" is the hardest part of fulfilling data subject requests. This underscores the importance of creating a comprehensive data map. Your map should address five key questions:
- What data is being collected?
- Why is it being processed?
- How is it handled?
- When is it erased?
- Who else has access to it?
Document every entry point for data, such as web forms, APIs, mobile apps, cookies, and third-party sources from vendors or partners. Then, trace the flow of data from collection to internal systems and external recipients. Don’t forget to identify where vendors operate and store data, as this will help you meet residency and sovereignty requirements.
"Data maps are the lynchpins of modern privacy." - Ethyca
Finally, complete your audit by confirming how long each type of data is retained.
Assess Data Retention Practices
Establish clear retention periods for every category of personal information and document the legal justification for keeping it - whether that’s a contractual obligation, legal requirement, or legitimate business need. The risk isn’t just holding onto data for too long; it’s also about "soft-deleted" data that lingers indefinitely in backups. During compliance audits, this still counts as retained data. In fact, organizations with audit-ready documentation report 40% less effort preparing for audits compared to those scrambling to gather evidence reactively.
Make sure you’re regularly verifying that data is removed from all storage locations, including backups. Don’t overlook unstructured data channels like email attachments and file-sharing platforms, as these often contain sensitive information that exists outside of formal database controls. And remember: even internal operations, like an EU subsidiary sharing data with a non-EU parent company, can qualify as an international transfer. In such cases, legal documentation is required to remain compliant.
Step 2: Establish a Legal Basis for Data Sharing
Once you've completed your data audit, the next step is to establish a solid legal foundation for sharing data. This step is critical to ensure compliance with privacy laws and maintain accountability. Before sharing any data with third parties, you need to identify and document the legal basis for doing so. As of April 2026, 20 states have enacted comprehensive data privacy laws, all of which require data sharing to rely on a valid legal basis. The appropriate basis will depend on your relationship with the individual and the purpose of the data sharing.
Determine Lawful Grounds for Data Sharing
There are several legal grounds for sharing data, including user consent, contractual necessity, legitimate interests, or legal obligations. Under laws like the CCPA/CPRA, most data sharing operates on an opt-out basis. However, sharing sensitive information - such as precise geolocation, genetic data, or neural data - requires opt-in consent.
For health-related data, HIPAA requires explicit authorization, and businesses must retain these forms for six years. Similarly, COPPA mandates verifiable parental consent for sharing data from children under 13.
If you plan to rely on legitimate interests, it’s essential to conduct and document a Legitimate Interests Assessment (LIA). This ensures that your business needs don’t unfairly override individual rights. Additionally, if data is shared with third parties outside the U.S., you must comply with cross-border frameworks like the EU-US Data Privacy Framework or use Standard Contractual Clauses (SCCs).
After determining the legal basis, ensure that all consents and agreements are thoroughly documented to maintain traceability during audits.
Document Consent and Agreements
Proper documentation is key once you've established your legal basis. Keep detailed records of the lawful grounds, the specific data being shared, and the third parties involved. For instance, under the CCPA, businesses are required to acknowledge consumer requests within 10 business days and fulfill them within 45 calendar days.
Neglecting proper consent documentation can lead to hefty fines. In March 2026, the California Privacy Protection Agency fined PlayOn Sports $1.10 million for improperly collecting and sharing personal data with advertising and social media partners without offering a compliant opt-out mechanism.
Your data processing agreements should explicitly prohibit the sale or unauthorized sharing of data beyond the defined business purpose. Privacy notices should clearly inform individuals about the data being shared, the parties involved, and the legal basis for sharing. If you're using automated decision-making technologies, be aware that new 2026 California regulations require businesses to provide notices and opt-out rights for data processed in this way.
Step 3: Develop and Enforce Data Processing Agreements
Once you've established your legal basis in Step 2, the next step is to create Data Processing Agreements (DPAs) with third-party vendors. These agreements clearly define roles, responsibilities, and safeguards for handling data, along with the steps to address any issues that arise. Keeping a close eye on how third parties handle your data is critical to closing the control gap identified earlier. Without a valid DPA, your organization could face serious penalties - under GDPR, this could mean fines of up to €10 million or 2% of your total global annual turnover.
DPAs act as the primary safeguard for shared data. They ensure clear accountability by outlining key details like the purpose of the data processing, the types of data involved, and the categories of individuals affected.
Key Clauses to Include in Agreements
To ensure compliance and reduce risk, your DPA should address a few crucial areas:
- Documented Instructions: Specify that processors can only act on your documented instructions. This prevents unauthorized or improper use of your data.
- Subprocessor Management: Detail whether vendors need general or specific approval to work with third parties. Require that subcontractors meet the same data protection standards. Typically, you’ll have a 30-day window to object to changes in subprocessors.
- Security Requirements: Lay out the exact technical and organizational measures required to protect data, such as encryption, access controls, and pseudonymization. For breach notifications, negotiate specific timelines (e.g., 24, 48, or 72 hours) instead of vague terms like "without undue delay."
- Data Subject Rights Support: Ensure the processor assists with Data Subject Access Requests (DSARs), including requests for access, rectification, or deletion. Set response times shorter than the standard one-month period required of controllers.
- Audit and Inspection Rights: Include provisions for audits, either through direct inspections or third-party certifications like SOC 2 or ISO 27001. If direct audits aren’t possible, require vendors to provide annual third-party audit reports.
- Deletion Protocols: Specify that all data, including backups, must be securely deleted upon contract termination. Require proof of deletion, such as a certificate of destruction or logs, with a typical timeline of 30 days.
- International Data Transfers: For data transfers to countries without adequacy decisions, include Standard Contractual Clauses or similar lawful mechanisms. For post-Brexit UK transfers, attach a UK Addendum to the EU SCCs.
Review and Update Contracts Regularly
Regulatory changes and operational shifts mean your agreements need regular updates. Review your DPAs frequently to ensure they reflect new vendor terms or legal requirements. If a vendor updates their standard terms of service, this is your cue to revisit and revise your DPA.
Keep DPAs as separate addendums rather than embedding them into your Master Service Agreement. This makes updates easier when laws change, as you won’t need to renegotiate the entire service contract. Use modular clauses and establish clear processes for handling changes, so your agreements stay flexible and compliant over time.
Step 4: Assess Third-Party Vendor Risks
Once your DPAs are set, the next step is to evaluate the risks associated with your third-party vendors. This ensures that these vendors comply with the critical security measures outlined in your data-sharing agreements. Between 2023 and 2024, 61% of companies faced a security breach linked to a third party, and by 2025, these breaches doubled year-over-year. As CISOSHARE aptly states, "Your security program is only as strong as your weakest vendor". This step helps pinpoint which vendors pose the highest risk and assess the protections they have in place to safeguard your data.
With DPAs enforced, it’s time to verify that vendor security measures match their contractual commitments. Start by categorizing vendors based on the type of data they access and the importance of their services. On average, companies work with around 237 vendors. High-risk vendors, such as those managing sensitive customer or financial data, should undergo quarterly reviews and thorough assessments. Medium-risk vendors may require annual evaluations, while low-risk suppliers can be reviewed every two to three years. This tiered approach ensures that critical partners get the attention they deserve without straining your resources.
Evaluate Vendor Security Certifications
Don’t just take vendors at their word - insist on independent verification of their security practices. For SaaS vendors, request SOC 2 Type II reports, which validate their controls over a 6–12-month period. Vendors handling credit card data must maintain PCI DSS compliance, while healthcare providers should demonstrate HIPAA compliance or hold a HITRUST CSF certification.
Always verify certifications through independent sources. For example, in early 2026, a ThirdProof investigation confirmed that Stripe achieved an A+ score on SSL/TLS analysis, with only two open ports and no CVEs, reflecting a minimal attack surface. In contrast, QuickBooks received an F (0/100) on HTTP security headers during the same period. If working with government contractors, verify their FedRAMP status directly on marketplace.fedramp.gov. After verifying certifications, establish ongoing oversight to address any new vulnerabilities that may arise.
Monitor Vendor Compliance Continuously
One-off assessments won’t cut it. 84% of organizations have experienced operational disruptions due to overlooked vendor risks. Implement event-driven reassessments that are triggered by specific incidents - such as a vendor experiencing a data breach, changes in ownership, or expanded access to your systems.
Additionally, leverage contractual audit rights under GDPR Article 28, which allow you to conduct inspections or request independent audits of vendor controls. For high-risk vendors, demand annual third-party audit reports and carry out joint incident response drills to test their breach notification processes. A 2026 investigation into payment provider Wise revealed multiple AML-related enforcement actions by the CFPB and international regulators, emphasizing the importance of monitoring regulatory actions and negative media coverage. Continuous vigilance ensures you stay ahead of potential risks.
Step 5: Implement Security and Access Controls
After conducting vendor risk assessments in Step 4, the next step is to secure your data with technical measures that go beyond contractual obligations. While contracts and certifications set expectations, technical controls ensure that data remains protected once it leaves your systems. As Marc ten Eikelder from Kiteworks explains:
"Sovereignty is maintained not because the vendor has made appropriate promises, but because the vendor has no technical capability to violate them".
This step emphasizes two key safeguards: encryption to keep your data unreadable without proper authorization and access controls to limit who can view or modify shared information. These measures help bridge the gap between vendor compliance and actual data security.
Enforce Data Encryption
Encryption is essential to protect your data both when it's being transmitted to third parties and when it's stored on their servers. However, not all encryption methods offer the same level of security. Many organizations opt for "Bring Your Own Key" (BYOK) solutions provided by major cloud vendors. With BYOK, you technically maintain ownership of the encryption keys, but the vendor's infrastructure still handles decryption. This means that under a legal subpoena, the vendor could be compelled to decrypt and provide readable data.
For highly sensitive information, a better option is customer-owned encryption keys. In this setup, vendors only hold encrypted data (ciphertext) and never have access to the decryption keys. As Kiteworks notes:
"The technical foundation is customer-owned encryption keys: when the data owner holds keys the vendor never possesses, the vendor cannot access or disclose readable content regardless of legal compulsion".
This approach aligns with the Digital Operational Resilience Act (DORA) requirements for encryption key management, which will take effect in 2025 for financial entities. To ensure robust encryption, your contracts should clearly define the encryption standards, key management processes, and whether the vendor has any decryption capability. While encryption protects against external threats, managing internal access is equally important.
Establish Access Control Protocols
Even with encrypted data, strict access controls are crucial to prevent unauthorized use - whether by your team or third-party personnel. Start by implementing role-based access control (RBAC), which ensures that users can only access the data necessary for their specific role. Following the principle of least privilege, a vendor’s support team troubleshooting payment issues, for instance, should not have access to customer contact information. This is especially critical given that 90% of enterprise data is unstructured, residing in emails, file shares, and collaboration tools rather than traditional databases.
To strengthen safeguards:
- Require multi-factor authentication (MFA) for all third-party access points.
- Log every access attempt, modification, and download.
- Ensure these logs are tamper-proof and provide a clear audit trail to comply with regulations like GDPR.
Additionally, schedule quarterly access reviews to identify and address any "permission drift" and immediately revoke access when vendor contracts end. By combining encryption with rigorous access controls, you can significantly reduce the risk of data misuse or breaches.
Step 6: Document and Monitor Data Sharing Practices
After setting up encryption and access controls in Step 5, the final step ensures that every decision around data sharing is both traceable and auditable. This involves documenting all data-sharing activities and regularly reviewing them to maintain compliance and address potential breaches. The ICO emphasizes the importance of this process:
"If agreements are not reviewed, there is a risk that they become inaccurate or inappropriate and could result in unlawful sharing or a data breach".
This step hinges on two critical tasks: keeping a detailed log of all data-sharing arrangements and conducting regular audits to confirm compliance. These measures form the foundation of ongoing adherence to legal requirements, bridging the gap between policy and practice. With the Data (Use and Access) Act taking effect on June 19, 2025, it’s vital that organizations align their documentation practices with the updated regulations.
Create a Data Sharing Log
A robust data-sharing log should include six key pieces of information for every third-party arrangement:
- What: Detail the data being shared and the legal basis for sharing it.
- Who: Identify the recipient, including their location and whether they are in third countries.
- Why: Document the purpose of sharing, the lawful basis for processing, and whether consent was obtained.
- How: Specify the transfer method and the type of relationship (e.g., controller-to-controller or controller-to-processor).
- When: Include retention periods and scheduled review dates.
- Compliance: Reference relevant Data Protection Impact Assessment (DPIA) reports and advice from your Data Protection Officer.
This log should connect seamlessly with your Record of Processing Activities (ROPA). Assign Information Asset Owners (IAOs) to oversee third-party transfer documentation within their respective areas. For large-scale data transfers, like those involving artificial intelligence services, implement tracking and labeling systems to maintain a clear understanding of data flows.
Schedule Routine Compliance Audits
Using the data-sharing log as a foundation, regular audits ensure that agreements remain accurate and relevant. Include review dates in the log to formalize this process.
During these audits, confirm that listed partner organizations are still operational and that the original reasons for data sharing are still valid. Automated discovery tools can help ensure that business processes align with documented agreements. Nimrod Vax from BigID highlights the importance of this:
"In today's increasingly continuous and real-time world, you have to be able to provide evidence that third-party data transfers are, in fact, consistent with the conditions of that legal contract".
Share audit results with your information governance board or senior management to address any compliance gaps swiftly and effectively.
Conclusion
Your compliance strategy must keep pace with shifting threats and evolving regulations. Third-party data sharing compliance is not a one-and-done task - it requires ongoing attention. With privacy laws continually changing, like the UK's Data (Use and Access) Act set to roll out in June 2025 and new privacy legislation across multiple U.S. states in 2025 and 2026, compliance needs to be treated as a dynamic process rather than a static checklist.
The consequences of non-compliance are steep. Under UK GDPR, violations can result in fines up to £17.5 million or 4% of global annual revenue - whichever is higher. But beyond avoiding penalties, there’s a clear business case for prioritizing privacy. As Nadia Benslimane, Marketing Specialist at Countly, puts it:
"Privacy is a competitive advantage rather than merely a compliance checkbox"
Organizations that prioritize strong data governance not only protect themselves but also earn customer trust, setting the stage for long-term growth.
The rapid rise of technologies like GenAI presents new challenges. A 2025 investigation found that 14% of employees regularly used GenAI tools on work devices, often bypassing approved logins. This creates compliance risks and security vulnerabilities that demand constant monitoring - not just periodic audits. Sub-processor changes and the growing use of GenAI tools make it clear: frequent reviews are essential.
For businesses looking to stay ahead of these challenges, the Top Consulting Firms Directory is a valuable resource. It connects organizations with experts in cybersecurity, risk management, and data analytics. These professionals can help implement technical safeguards, navigate overlapping regulations, and set up compliance systems that grow with your business.
While the six-step checklist lays the groundwork, true compliance requires more than just ticking boxes. Leadership buy-in, continuous staff training, and adaptability to new regulations are essential. Start with a thorough data audit, establish clear legal frameworks, and document everything carefully - this preparation will make future regulatory shifts far easier to handle.
FAQs
How do I decide whether a vendor is high-risk?
To figure out if a vendor poses a high risk, start with a vendor risk assessment. Pay close attention to areas like data access, security controls, and their compliance history. Vendors that handle a lot of sensitive data, have weak security practices, or show past compliance problems are more likely to be high-risk. It's also essential to evaluate the potential fallout from a breach or failure and pinpoint any gaps in their controls to judge how well they can safeguard your data and operations.
When do I need consent vs. legitimate interest to share data?
When sharing personal data, consent is mandatory for purposes that require explicit permission - like handling sensitive information or specific, clearly defined uses. On the other hand, legitimate interest can serve as a basis for processing data if it’s essential for your organization’s goals, doesn’t infringe on individuals’ rights, and passes a balancing test to weigh the benefits against potential risks.
Regardless of the basis, it’s crucial to keep data subjects informed to maintain transparency and trust.
What should I track in a data-sharing log?
To maintain compliance and ensure accountability, a data-sharing log should cover the following details:
- Purpose of sharing: Clearly state why the data is being shared.
- Type and scope of data shared: Specify what kind of data is being shared and its extent.
- Parties involved: Identify all entities or individuals participating in the data exchange.
- Date and time of sharing: Record when the data was shared.
- Sharing method: Document how the data was transferred (e.g., email, secure portal).
- Safeguards in place: Note the measures taken to protect the data during sharing.
- Legal justifications or exemptions: Include the legal basis or any applicable exceptions.
- Roles and responsibilities: Outline what each party is responsible for in the process.
Keeping such detailed records helps ensure lawful data handling, facilitates audits, and builds trust through greater transparency.


