Organizations moving to the cloud must ensure their security measures align with ISO 27001, the global standard for managing information security. The 2022 update to ISO 27001 modernized its controls, emphasizing cloud services and shared responsibility between providers and customers. With the October 2025 deadline to transition to the updated standard, understanding how ISO 27001 applies to multi-cloud and hybrid cloud models is critical.
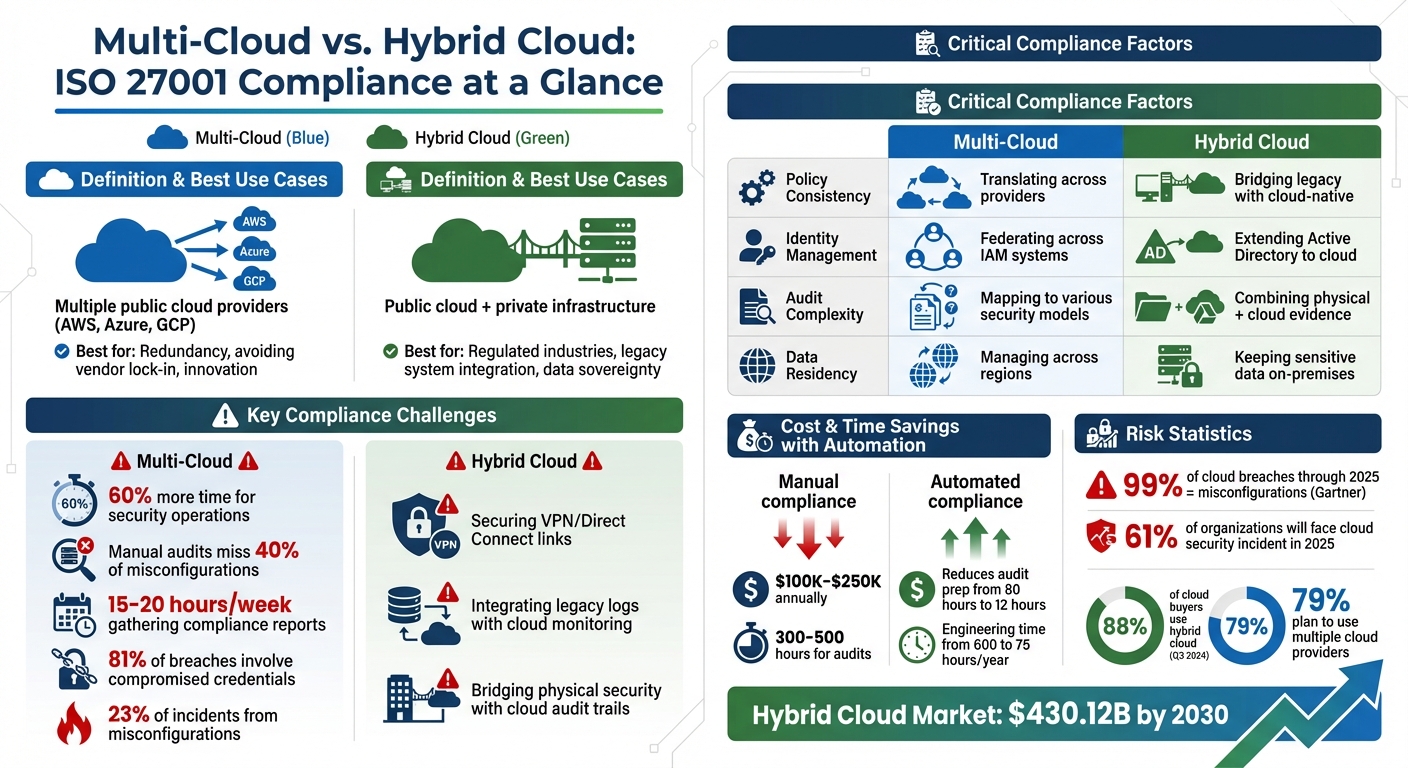
- Multi-cloud: Involves using multiple public cloud providers like AWS, Azure, or GCP. It offers resilience and flexibility but creates complexities in unifying security policies across platforms.
- Hybrid cloud: Combines public cloud services with private infrastructure. It’s ideal for sensitive workloads but requires integrating legacy systems with cloud-native controls.
Both models face challenges in compliance, such as configuration drift, identity management, and audit preparation. Automated tools and continuous monitoring can simplify the certification process and reduce costs, but the choice of cloud strategy depends on your organization's goals, regulatory needs, and operational priorities.
Quick Overview:
- Multi-cloud: Best for redundancy and avoiding vendor lock-in.
- Hybrid cloud: Best for regulated industries and legacy system integration.
Compliance requires balancing shared responsibilities and implementing consistent security baselines across environments.
Multi-Cloud vs Hybrid Cloud ISO 27001 Compliance Comparison
ISO 27001 Compliance: Multi-Cloud vs. Hybrid Cloud
Core ISO 27001 Requirements for Cloud Environments
ISO 27001's Annex A 5.23 emphasizes the need for structured processes to handle the lifecycle of cloud services - acquisition, management, and retirement. This requirement applies to both multi-cloud and hybrid cloud setups, though the way it's implemented varies.
A key part of cloud compliance lies in the shared responsibility model. Here’s the breakdown: cloud providers handle the security of the infrastructure (think physical servers, networks, and hypervisors), while you’re responsible for securing what you build on top - like data, configurations, access controls, and applications. In hybrid environments, this responsibility expands, as you must secure both cloud-based resources and on-premises systems.
Several other controls are critical for compliance:
- A.8.9: Configuration management to detect and address drift.
- A.8.15: Comprehensive logging for monitoring and auditing.
- A.8.24: Encryption for data both at rest and in transit.
- A.15: Managing supplier relationships effectively.
While these controls apply to both multi-cloud and hybrid setups, the strategies for implementation differ significantly between the two.
Main Differences in Compliance Approaches
In multi-cloud environments, the challenge lies in unifying security policies across platforms. Each cloud provider - AWS, Azure, and GCP - comes with its own set of identity management systems, APIs, and terminology. For example, AWS uses IAM roles, Azure relies on RBAC, and GCP has its identity model. This complexity means multi-cloud setups demand 60% more time for security operations, and manual audits can miss up to 40% of misconfigurations.
"Choosing multiple clouds for resilience creates security complexity that can become your biggest vulnerability." - Zsoftly Editorial
On the other hand, hybrid cloud compliance involves integrating traditional on-premises controls with modern cloud-native security measures. The connection between your on-prem data center and the cloud - whether through VPN or Direct Connect - becomes a critical vulnerability point. This setup requires managing two distinct security paradigms: extending legacy systems like Active Directory to the cloud while also implementing cloud-native security controls.
A major risk in multi-cloud environments is configuration drift. For instance, a manual change made in the AWS console that bypasses your Infrastructure as Code (IaC) workflow can lead to inconsistencies, which auditors are likely to flag. Security teams in multi-cloud setups often spend 15–20 hours per week gathering data for compliance reports.
Compliance Comparison Table
| Factor | Multi-Cloud | Hybrid Cloud |
|---|---|---|
| Policy Consistency | Translating a single baseline across multiple providers (AWS, Azure, GCP) | Bridging legacy on-prem policies with cloud-native controls |
| Audit Complexity | High; mapping ISO 27001 to various provider-specific security models | High; combining physical security evidence with cloud-based logs |
| Data Residency Controls | Managing data placement across regions to meet GDPR or sovereignty rules | Often keeps sensitive data on-premises for stricter residency compliance |
| Vendor Risk Management | Handling contracts and SLAs with multiple cloud providers simultaneously | Managing secure connections between on-prem systems and a single cloud provider |
| Identity Management | Federating identities across multiple IAM systems (AWS IAM, Azure RBAC, GCP IAM) | Extending on-prem identity systems like Active Directory to the cloud |
| Visibility & Monitoring | Aggregating logs and alerts from diverse cloud APIs | Integrating on-prem logs with cloud monitoring tools |
sbb-itb-97f6a47
Security and Risk Management Considerations
Hybrid Cloud Security: Benefits and Challenges
Hybrid cloud setups strike a balance by keeping sensitive data on private infrastructure while moving less critical workloads to the public cloud. This model offers scalability and flexibility while helping meet strict data residency rules or support legacy systems that aren’t cloud-ready.
However, securing hybrid environments requires a mix of traditional data center defenses and modern cloud-native controls. One key challenge is safeguarding critical connections between on-premises systems and the cloud. Another involves managing legacy identity systems alongside cloud-native tools, which can complicate access management.
Log integration is another sticking point. Legacy firewall and server logs need to work seamlessly with modern cloud monitoring tools, creating additional hurdles for ISO 27001 compliance reporting. Bridging physical security evidence, like data center access logs, with cloud-based audit trails further adds to the complexity.
While hybrid clouds pose these challenges, multi-cloud environments bring their own set of risks.
Multi-Cloud Security Risks
Multi-cloud environments inherently expand the attack surface. Each added cloud provider introduces new APIs, entry points, and cross-cloud communication channels that must be secured. Statistics show that 81% of cloud-related breaches involve compromised credentials, with 23% of public cloud security incidents caused by misconfigurations. As the environment grows more complex, so do the risks.
Policy fragmentation is a major issue. Each provider - AWS, Azure, and GCP - has its own identity model, such as IAM roles, RBAC, or other frameworks. This leads to "identity sprawl", where service accounts across providers increase the likelihood of orphaned credentials and over-permissioned accounts.
"Most security practitioners feel more at home in one cloud than the others, and they may feel really good about one of them, but they do not have the same level of confidence about the others".
Visibility is another challenge. With multiple dashboards to monitor, teams often spend 2–3 hours daily manually correlating security findings when relying solely on native tools. Addressing these risks is vital for aligning multi-cloud strategies with ISO 27001 standards.
Security and Risk Management Comparison Table
Here’s a quick breakdown of the security and risk management differences between multi-cloud and hybrid cloud setups:
| Security Aspect | Multi-Cloud | Hybrid Cloud |
|---|---|---|
| Primary Risk | Fragmented policies and configuration drift across providers | Securing VPN/Direct Connect link between on-premises and public cloud |
| Attack Surface | Multiple APIs, entry points, and cross-cloud channels | Critical connection point between private and public infrastructure |
| Identity Challenge | Federating identity across multiple cloud IAM systems | Extending on-premises identity systems to the cloud |
| Visibility Issue | Aggregating logs from distinct cloud APIs | Integrating legacy on-premises logs with cloud monitoring |
| Skills Gap | Deep expertise in one provider, limited in others | Expertise in both data center security and cloud-native controls |
| Data Protection | Securing data movement between providers and regions | Maintaining sensitive workloads on private infrastructure |
| Mitigation Strategy | Central IdP for federated access; CSPM for unified visibility | Secure connection architecture; bridge legacy controls with cloud automation |
How to Achieve ISO 27001 Certification
Multi-Cloud Compliance Steps
To align with ISO 27001 in a multi-cloud setup, start by creating a unified baseline framework. This involves mapping all provider-specific controls - whether from AWS, Azure, or GCP - to ISO 27001 standards. Tools like Open Policy Agent can help enforce compliance by implementing Policy-as-Code. These tools scan Infrastructure as Code templates before deployment, ensuring that non-compliant configurations are caught early, before they reach production environments.
Streamline audit preparation by automating evidence collection. This can reduce the preparation time from 80 hours to just 12 hours. Tools such as AWS Audit Manager or Prowler can generate timestamped, immutable records for every policy evaluation. To simplify management, use a unified Cloud Security Posture Management (CSPM) platform. This consolidates findings from AWS Security Hub, Azure Defender, and GCP Security Command Center into a single dashboard, saving security teams 15–20 hours per week that would otherwise be spent manually correlating findings across platforms.
Switch from traditional point-in-time audits to Continuous Control Monitoring. This real-time strategy helps identify compliance drift as soon as it occurs, ensuring that all cloud environments remain aligned with ISO 27001 standards.
Hybrid Cloud Compliance Steps
Hybrid cloud environments require a different strategy for ISO 27001 certification. Start by inventorying legacy on-premises assets and mapping how data flows between these systems and the cloud. Clearly document which controls are inherited from your on-premises data center - such as physical security - and which are managed in the cloud, like Identity and Access Management (IAM) and encryption. This documentation is critical for meeting Control A.5.23, introduced in the 2022 ISO 27001 update.
Secure connectivity between on-premises and cloud systems is vital. Use VPNs or Direct Link connections and deploy on-premises agents for centralized scanning. To address integration challenges, standardize encryption and access controls. For example, define a policy like "AES-256 for all data at rest" and map it to specific implementations, such as AWS KMS for cloud workloads and Transparent Data Encryption for on-premises databases. Extend your on-premises identity systems to the cloud using federated access, and enforce multi-factor authentication across both environments consistently.
Regularly conduct tabletop exercises and incident response drills. These exercises test failover capabilities between on-premises and cloud systems, ensuring that both Recovery Time Objective (RTO) and Recovery Point Objective (RPO) are met.
Implementation Steps Comparison Table
| Implementation Phase | Multi-Cloud Specific Actions | Hybrid Cloud Specific Actions |
|---|---|---|
| Assessment | Map controls to ISO 27001 baseline. | Inventory assets and map data flows. |
| Design | Define cross-cloud IAM and logging. | Establish secure connectivity. |
| Migration | Deploy IaC with security guardrails. | Integrate on-premises agents. |
| Optimization | Implement Continuous Control Monitoring. | Conduct failover drills. |
Navigating ISO 27001 and Multi-Cloud with Security Architect Gabor Sivók
Use Cases and Decision-Making Framework
Let’s expand on earlier compliance insights by exploring how different cloud models can be applied in specific scenarios. This guidance will help you decide which option aligns best with your organization’s needs.
When to Use Hybrid Cloud
Hybrid cloud is ideal for organizations bound by strict regulatory requirements or those relying on legacy infrastructure. Industries like finance, healthcare, and government often need to keep sensitive data on-premises or within specific jurisdictions to comply with ISO 27001’s data sovereignty standards. For example, banks might store customer financial data in private data centers while using public cloud platforms for customer-facing mobile apps. Manufacturing and mining operations also benefit from hybrid setups, as they require low-latency processing that public clouds alone cannot provide.
This model is particularly useful for organizations with significant on-premises investments. It allows for gradual modernization while ensuring compliance with ISO 27001 controls. Hybrid cloud supports integration with legacy systems while maintaining control over sensitive assets. The market for hybrid cloud reflects its appeal, with projections estimating it will reach nearly $430.12 billion by 2030, driven largely by demand from regulated industries.
When to Use Multi-Cloud
Multi-cloud strategies align well with ISO 27001’s focus on business continuity and risk management by offering redundancy across multiple vendors. If one provider’s control plane fails, operations can continue seamlessly on another platform. Organizations prioritizing resilience, cost efficiency, and flexibility often choose multi-cloud to access best-in-class services. For instance, AWS might be used for computing power, Google Cloud Platform for AI tools, and Azure for DevOps.
This approach is also valuable for businesses operating across multiple regions. Selecting data centers in specific countries helps meet local compliance requirements. By Q3 2024, 88% of cloud buyers are expected to use hybrid cloud environments, and 79% plan to leverage multiple cloud providers. Multi-cloud is especially effective when innovation and access to specialized services take precedence over physical infrastructure control.
Choosing the Right Cloud Model
Selecting the right cloud model starts with evaluating your critical assets and compliance priorities. If you operate in highly regulated sectors such as finance or healthcare, rely on legacy systems, or face stringent data residency rules, hybrid cloud is likely your best option. On the other hand, if avoiding vendor lock-in, achieving provider redundancy, or leveraging specialized tools are your main goals, multi-cloud might be the better fit.
Regardless of your choice, it’s crucial to establish a consistent security baseline across private and public clouds to meet ISO 27001 standards. Adopting Zero Trust principles - where every user and system is treated as "untrusted" by default - can significantly reduce vulnerabilities. It’s worth noting that Gartner predicts 99% of cloud breaches through 2025 will result from misconfigurations or compliance oversights.
| Scenario | Recommended Model | Rationale |
|---|---|---|
| Highly Regulated Data (Finance, Healthcare) | Hybrid Cloud | Keeps sensitive data isolated on-premises while enabling cloud-based analytics. |
| Innovation & Best-of-Breed (AI, ML, Analytics) | Multi-Cloud | Provides access to specialized tools without being tied to a single vendor. |
| Steady-State Workloads (ERP, Core Databases) | Hybrid (Private Anchor) | Offers predictable costs and consistent performance. |
| Global Jurisdictions (Data Sovereignty) | Multi-Cloud | Allows selection of data centers in various regions to comply with local laws. |
| Legacy System Modernization | Hybrid Cloud | Supports phased migration without requiring a complete cloud rewrite. |
Conclusion and Expert Resources
Key Takeaways
Navigating ISO 27001 compliance in cloud environments is no small task. Certification isn’t something you can inherit directly from your cloud provider - even if they’re certified, you’re still responsible for securing your own environment and managing risks tailored to your operations. The shared responsibility model is at the core of both multi-cloud and hybrid cloud compliance. Providers handle the infrastructure, but you’re in charge of critical areas like data classification, identity and access management (IAM), and encryption.
Multi-cloud setups add even more complexity because security models differ across vendors. For example, vendor-specific IAM actions often require security teams to spend significant time reconciling inconsistencies. These environments can also increase workloads, with manual audits missing up to 40% of misconfigurations. On the other hand, hybrid cloud compliance demands integrating legacy on-premises systems with modern cloud controls - tasks like aligning physical firewall rules with virtual security groups or deploying local collectors for visibility can be particularly challenging.
Automation is becoming a must-have. Without it, manual compliance efforts can cost between $100,000 and $250,000 annually and consume 300–500 hours just for audit preparation. However, adopting Compliance-as-Code and continuous monitoring can cut internal engineering time from about 600 hours to just 75 per year. And with 61% of organizations expected to face at least one cloud-related security incident in 2025 - often due to gaps in shared responsibility or multi-tenancy issues - tools like real-time monitoring and policy-as-code frameworks are critical to staying compliant between audits.
These insights underline the importance of expert guidance to ensure your compliance strategy aligns seamlessly with your operational needs.
Find Expert Consulting Support
Many internal teams lack the specialized expertise needed to tackle these challenges. One cloud architect summed it up perfectly:
"We have three cloud experts, but they spend more time explaining differences between AWS IAM, Azure RBAC, and GCP IAM to each other than actually securing our infrastructure".
This is where expert consultants come in. They bring the in-depth knowledge needed to clarify shared responsibility, simplify certification processes, and design compliance strategies that fit your business.
If you’re looking for help, the Top Consulting Firms Directory is a great starting point. It connects you with firms specializing in ISO 27001 compliance, cloud security, and IT strategy. These firms offer expertise in areas like digital transformation, cybersecurity, IT infrastructure, and risk management. Whether you need to establish a unified compliance baseline across AWS, Azure, and GCP or need help integrating on-premises controls with cloud-native security, consultants can provide the automation frameworks, continuous monitoring, and audit readiness support that manual processes simply can’t match.
FAQs
What’s the fastest way to map AWS, Azure, and GCP controls to ISO 27001?
The quickest way to align AWS, Azure, and GCP controls with ISO 27001 is by using automation tools and detailed mapping guides designed for multi-cloud setups. Take advantage of compliance resources, such as provider-specific guides for AWS, Azure, and GCP. These guides often include step-by-step instructions and ready-to-use templates that make the process easier. Additionally, automation frameworks can streamline tasks like monitoring and documentation, cutting down on manual work while helping you stay in line with ISO 27001 standards.
How do we prove shared responsibility to an ISO 27001 auditor?
To establish shared responsibility, it’s crucial to clearly define and communicate the roles of your organization and your cloud provider. Use a shared responsibility model to outline who handles key aspects such as physical security, infrastructure management, access controls, and data protection. Back up these responsibilities with evidence - this could include policies, control mappings, or audit trails.
Maintaining transparency, keeping detailed documentation, and conducting regular monitoring are critical steps to show compliance during an ISO 27001 audit.
Which tools best automate ISO 27001 evidence collection across clouds?
When it comes to automating ISO 27001 evidence collection in multi-cloud environments, certain tools stand out for simplifying the process. Solutions like SureCloud, SecureSlate, and Complimetric are designed specifically for multi-cloud setups, offering features that automate evidence gathering, enforce policies, and monitor systems continuously.
Additionally, Cloud Security Posture Management (CSPM) tools play a key role by handling automated compliance checks, generating evidence, and detecting configuration drifts. These tools not only minimize manual work but also help maintain audit readiness while integrating smoothly with various cloud providers.


